VNC IoT Behind Firewall on Mac: Troubleshooting and Solutions
Are you struggling with VNC IoT behind firewall issues on your Mac? You're not alone. Many users face challenges when trying to establish a secure connection through firewalls for remote access. This article will guide you through understanding the problem and provide effective solutions.
Remote desktop connections are an essential tool for modern businesses and individuals alike. Whether you're managing IoT devices or accessing your office computer from home, VNC (Virtual Network Computing) plays a crucial role. However, firewalls can sometimes block these connections, leading to frustration and inefficiency.
By the end of this article, you'll have a comprehensive understanding of why VNC IoT connections might fail behind firewalls on Mac and how to resolve these issues. Let's dive in!
Introduction to VNC IoT Behind Firewall
VNC IoT behind firewall issues on Mac can be a significant hurdle for users who rely on remote access. VNC is a widely used protocol for controlling remote computers and IoT devices. When working within a network protected by a firewall, establishing a VNC connection can become problematic.
The primary function of a firewall is to protect your network from unauthorized access. However, this protection can sometimes block legitimate VNC connections, especially when the firewall is not configured correctly.
Understanding the interaction between VNC, IoT devices, and firewalls is crucial for troubleshooting and resolving connection issues. This section will provide an overview of the challenges faced and why they occur.
Understanding Firewalls and Their Role
A firewall acts as a barrier between your internal network and the external world. It monitors and controls incoming and outgoing network traffic based on predetermined security rules.
Types of Firewalls
- Packet-filtering firewalls
- Stateful inspection firewalls
- Application-level gateways
- Next-generation firewalls
Each type of firewall has its own strengths and weaknesses. For VNC IoT connections, the configuration of the firewall is critical. Incorrect settings can block necessary ports or protocols, leading to connection failures.
Common Issues with VNC IoT Behind Firewalls
There are several common issues that users encounter when trying to establish VNC IoT connections behind firewalls on Mac:
- Port Blocking: Firewalls often block the default VNC port (5900) to prevent unauthorized access.
- IP Address Restrictions: Some firewalls restrict access based on IP addresses, preventing connections from unknown sources.
- Protocol Restrictions: Certain firewalls may block the VNC protocol entirely.
Identifying the specific issue is the first step toward resolving it. Understanding the nature of the problem will help in selecting the appropriate solution.
Diagnosing the Problem
Before attempting any solutions, it's essential to diagnose the problem accurately. Here are some steps you can take:
- Check the firewall logs for any blocked connections.
- Test the VNC connection from outside the firewall to determine if the issue is firewall-related.
- Verify that the necessary ports are open and accessible.
Using tools like Nmap can help identify open ports and potential issues with your network configuration.
Effective Solutions
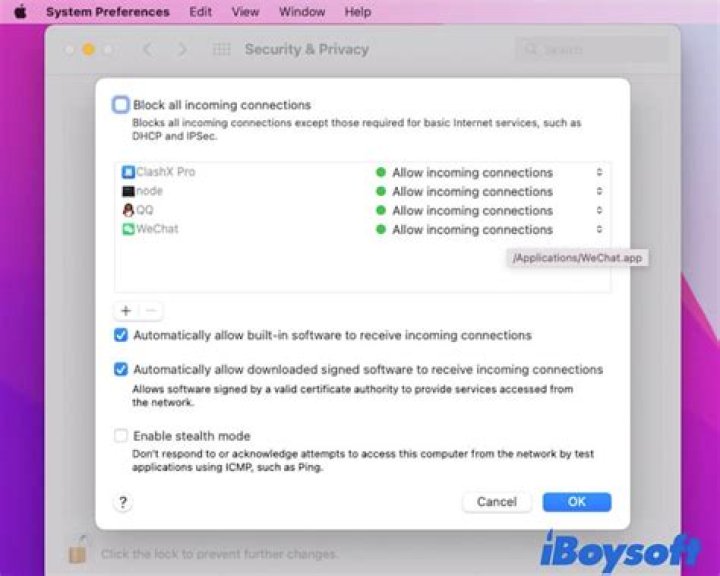
1. Configure Firewall Rules
Adjusting the firewall rules to allow VNC traffic is often the simplest solution. Ensure that the necessary ports are open and that the VNC protocol is permitted.
2. Use a Different Port
If the default VNC port is blocked, consider using a different port for your connection. This can be configured in the VNC settings on both the client and server sides.
3. Implement a Proxy Server
A proxy server can act as an intermediary between your Mac and the IoT device, bypassing firewall restrictions. This method requires careful setup and configuration.
Advanced Techniques for Secure Connections
For users requiring more advanced solutions, consider the following techniques:
- VPN: A Virtual Private Network can provide a secure tunnel through the firewall, allowing VNC connections.
- SSH Tunneling: Secure Shell tunneling encrypts the VNC traffic, making it more secure and less likely to be blocked.
- Port Forwarding: Configuring your router to forward VNC traffic to the correct internal IP address can help bypass firewall restrictions.
These methods require a higher level of technical expertise but offer greater flexibility and security.
Best Practices for VNC IoT Setup
To ensure a smooth and secure VNC IoT setup, follow these best practices:
- Regularly update your VNC software to the latest version.
- Use strong passwords and authentication methods.
- Limit access to trusted IP addresses whenever possible.
Adhering to these practices will help minimize security risks and improve the reliability of your VNC connections.
Security Considerations
Security is paramount when dealing with VNC IoT connections. Firewalls are designed to protect your network, but they can also inadvertently block legitimate traffic. Balancing security with functionality is key.
Encryption
Always use encrypted connections to protect sensitive data. VNC supports various encryption methods, including SSL/TLS, which can enhance the security of your connections.
Regular Audits
Conduct regular audits of your firewall rules and network configuration to ensure they align with your security policies.
Troubleshooting Tips
If you continue to experience issues with VNC IoT behind firewall on Mac, try these troubleshooting tips:
- Check for software updates for both VNC and your firewall.
- Consult the documentation for your specific firewall model.
- Reach out to your network administrator or IT support for assistance.
Remember, persistence and methodical troubleshooting are often the keys to resolving complex network issues.
Conclusion
VNC IoT behind firewall issues on Mac can be challenging, but with the right knowledge and tools, they are solvable. By understanding the role of firewalls, diagnosing the problem accurately, and implementing effective solutions, you can ensure smooth and secure remote access.
We encourage you to share your experiences and solutions in the comments below. Your insights could help others facing similar challenges. Additionally, explore our other articles for more tips and tricks on network security and remote access.
For further reading, consider the following resources: