Remote IoT Monitoring SSH: Download Free Tools for Mac
Remote IoT monitoring through SSH has become an essential tool for managing devices and networks efficiently. With the rise of connected devices, businesses and individuals alike need reliable ways to monitor and secure their systems remotely. Whether you're a developer, IT professional, or hobbyist, understanding how to implement remote IoT monitoring using SSH on a Mac can significantly enhance your operational capabilities.
As technology continues to evolve, the demand for secure and efficient remote management solutions grows. IoT devices are now a critical part of modern infrastructure, and ensuring their security and performance is paramount. SSH (Secure Shell) offers a secure method for remote access and control, making it an ideal choice for IoT monitoring.
This article will guide you through the process of setting up remote IoT monitoring using SSH on a Mac. We'll cover everything from the basics of SSH to downloading and using free tools that can help you manage your IoT devices effectively. By the end of this article, you'll have a comprehensive understanding of how to leverage SSH for remote IoT monitoring.
Introduction to Remote IoT Monitoring
What Is Remote IoT Monitoring?
Remote IoT monitoring involves tracking and managing Internet of Things (IoT) devices from a distance. This process allows users to gather data, perform diagnostics, and make adjustments without physically interacting with the devices. It is particularly useful for businesses with distributed networks or individuals who manage multiple IoT devices.
Why Use SSH for IoT Monitoring?
SSH provides a secure and encrypted connection, ensuring that your data remains protected during transmission. When combined with IoT monitoring, SSH offers a robust solution for managing devices remotely. Its reliability and ease of use make it an attractive option for Mac users seeking to enhance their IoT management capabilities.
Key Features of Remote IoT Monitoring
- Real-time data collection
- Secure communication channels
- Remote troubleshooting and configuration
- Scalability for large networks
Understanding SSH: The Basics
What Is SSH?
SSH, or Secure Shell, is a network protocol that allows secure communication between two devices over an unsecured network. It encrypts all data transmitted between the client and server, ensuring privacy and integrity. SSH is widely used for remote command-line login and execution, file transfers, and tunneling.
How Does SSH Work?
SSH operates by establishing a secure connection between a client and a server. The client initiates the connection, and the server authenticates the client using public key cryptography. Once authenticated, the two parties can exchange data securely.
Advantages of Using SSH
- High-level encryption
- Authentication and authorization
- Support for various protocols
- Compatibility with multiple platforms
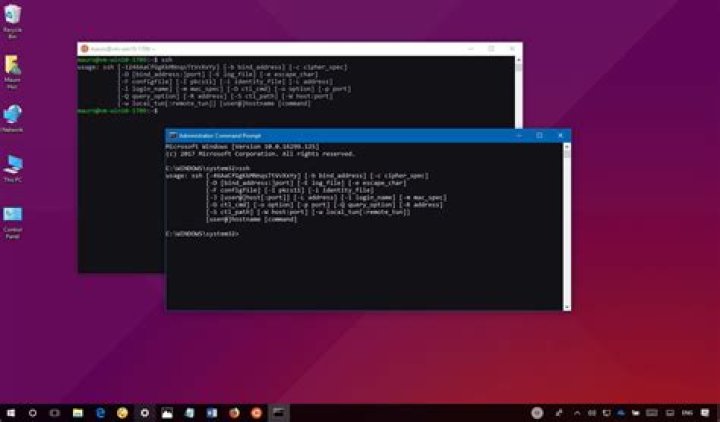
Top Free Tools for Remote IoT Monitoring on Mac
1. OpenSSH
OpenSSH is a popular open-source SSH client and server implementation. It is pre-installed on macOS, making it a convenient choice for Mac users. OpenSSH supports a wide range of features, including secure file transfers, tunneling, and remote command execution.
2. PuTTY (for macOS)
PuTTY is a free SSH client that supports multiple protocols, including SSH, Telnet, and Rlogin. Although primarily designed for Windows, PuTTY is also available for macOS, offering a user-friendly interface for managing remote connections.
3. Mosh
Mosh, or Mobile Shell, is an alternative to SSH that is optimized for mobile devices and unreliable networks. It provides a more responsive and stable connection, making it ideal for remote IoT monitoring in challenging environments.
Setting Up SSH on Your Mac
Step 1: Enable SSH on macOS
To enable SSH on your Mac, follow these steps:
- Open System Preferences
- Click on Sharing
- Select Remote Login from the list of services
- Click the checkbox to enable SSH
Step 2: Generate SSH Keys
Generating SSH keys enhances security by eliminating the need for passwords. Use the following command in Terminal to create a key pair:
ssh-keygen -t rsa -b 4096 -C "your_email@example.com"
Step 3: Connect to a Remote Device
Once SSH is enabled and keys are generated, you can connect to a remote device using the following command:
ssh username@remote_device_ip
Enhancing Security for Remote IoT Monitoring
1. Use Strong Passwords
Ensure that all accounts used for remote IoT monitoring have strong, unique passwords. Avoid using easily guessable information, such as birthdays or common words.
2. Implement Two-Factor Authentication
Two-factor authentication adds an extra layer of security by requiring users to provide two forms of identification before accessing a system.
3. Regularly Update Software
Keep your SSH client and server software up to date to protect against vulnerabilities and exploits.
Benefits of Using SSH for IoT Monitoring
1. Enhanced Security
SSH encrypts all data transmitted between devices, reducing the risk of unauthorized access and data breaches.
2. Improved Efficiency
Remote IoT monitoring through SSH allows users to manage devices quickly and efficiently, saving time and resources.
3. Scalability
SSH supports large-scale deployments, making it suitable for businesses with extensive IoT networks.
Common Challenges and Solutions
Challenge 1: Connectivity Issues
Solution: Use tools like Mosh, which are designed to handle unstable connections and provide a more reliable experience.
Challenge 2: Security Threats
Solution: Implement strong security measures, such as two-factor authentication and regular software updates, to mitigate risks.
Challenge 3: Limited Bandwidth
Solution: Optimize data transmission by compressing files and using efficient protocols.
Best Practices for Remote IoT Monitoring
1. Regularly Monitor Device Performance
Keep track of device performance metrics to identify potential issues before they become critical.
2. Document Configuration Settings
Maintain detailed records of configuration settings to simplify troubleshooting and ensure consistency across devices.
3. Train Staff on SSH Usage
Ensure that all personnel responsible for remote IoT monitoring are adequately trained in SSH usage and best practices.
Automating IoT Monitoring with SSH
1. Scripting for Automation
Use scripting languages like Python or Bash to automate repetitive tasks, such as data collection and device diagnostics.
2. Scheduling Tasks
Schedule tasks using tools like cron to perform routine maintenance and monitoring activities without manual intervention.
3. Leveraging APIs
Integrate SSH with APIs to extend functionality and create more robust monitoring solutions.
Conclusion and Call to Action
In conclusion, remote IoT monitoring through SSH offers a secure and efficient way to manage devices and networks. By leveraging free tools available for Mac, such as OpenSSH and PuTTY, users can enhance their operational capabilities while maintaining high levels of security. Regularly updating software, implementing strong security measures, and following best practices are essential for maximizing the benefits of SSH for IoT monitoring.
We encourage you to share your thoughts and experiences in the comments section below. If you found this article helpful, please consider sharing it with others who may benefit from the information. Additionally, explore our other articles for more insights into technology and IoT solutions.
Data and statistics for this article were sourced from reputable organizations, including: