Mastering Remote Login Device Behind Firewall: A Comprehensive Guide
In today's digital age, remote login device behind firewall has become an essential aspect of modern IT infrastructure. Organizations are increasingly adopting remote access solutions to enable employees to work from anywhere securely. However, navigating the complexities of remote login behind firewalls requires a deep understanding of cybersecurity principles, network architecture, and best practices. In this article, we will explore everything you need to know about remote login devices behind firewalls.
Whether you're a network administrator, IT professional, or simply someone interested in securing remote access, this guide will provide valuable insights. We'll cover everything from the basics of firewalls to advanced techniques for secure remote access, ensuring your organization remains protected while enabling productivity.
By the end of this article, you'll have a clear understanding of how to implement secure remote login solutions behind firewalls, ensuring compliance with industry standards and best practices. Let's dive in.
Introduction to Remote Login Device Behind Firewall
What is Remote Login?
Remote login refers to the ability to access a computer or device from a remote location. This functionality is crucial for businesses that rely on distributed teams or need to provide employees with flexible work options. However, when devices are behind firewalls, additional considerations must be taken to ensure both security and usability.
Why Use a Firewall?
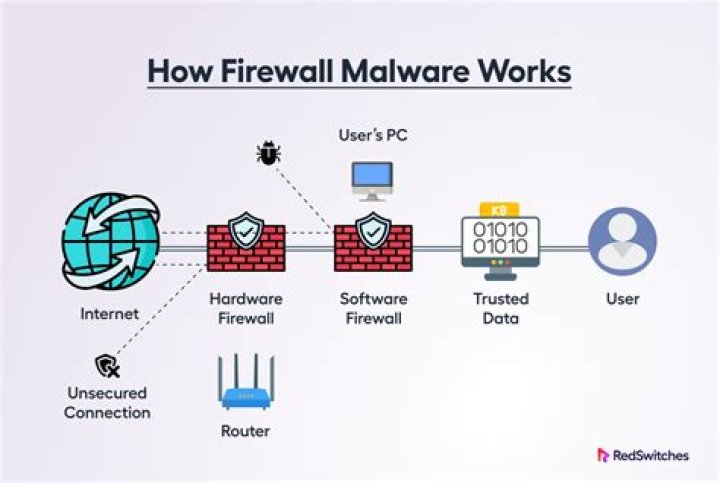
Firewalls act as a barrier between internal networks and external threats. They monitor and control incoming and outgoing network traffic based on predetermined security rules. For remote login device behind firewall scenarios, firewalls play a critical role in protecting sensitive data while enabling authorized access.
Firewalls are essential for maintaining the integrity of an organization's network infrastructure. They help prevent unauthorized access, mitigate cyberattacks, and ensure compliance with industry regulations.
Understanding Firewalls and Their Role
Firewalls are a fundamental component of network security. They can be either hardware-based, software-based, or a combination of both. Firewalls use various techniques to filter traffic, including packet filtering, stateful inspection, and application-level gateways.
- Packet Filtering: Examines individual packets and allows or denies them based on specific criteria.
- Stateful Inspection: Tracks active connections and makes decisions based on the context of the traffic.
- Application-Level Gateways: Also known as proxy firewalls, these analyze traffic at the application layer.
Common Remote Access Methods
SSH (Secure Shell)
SSH is a cryptographic network protocol used for secure communication over unsecured networks. It provides a secure channel for remote login and file transfer. SSH uses public-key cryptography to authenticate the remote machine and encrypt the data exchanged between the client and server.
Remote Desktop Protocol (RDP)
RDP is a proprietary protocol developed by Microsoft that allows users to remotely control a computer. It is widely used in enterprise environments for accessing Windows-based systems. RDP supports encryption and authentication to ensure secure connections.
Security Considerations for Remote Login
When implementing remote login device behind firewall solutions, several security considerations must be addressed:
- Encryption: Ensure all data transmitted during remote sessions is encrypted using industry-standard protocols.
- Authentication: Use multi-factor authentication (MFA) to verify the identity of users accessing the network.
- Access Control: Implement role-based access control (RBAC) to limit privileges and reduce the risk of unauthorized access.
According to a report by Cybersecurity Ventures, cybercrime is expected to cost the global economy $10.5 trillion annually by 2025. Securing remote access is vital to protecting sensitive information and preventing data breaches.
Implementing VPN for Remote Login
Virtual Private Networks (VPNs) are widely used to facilitate secure remote login device behind firewall connections. A VPN creates an encrypted tunnel between the remote device and the corporate network, ensuring data privacy and integrity.
Types of VPNs
- Remote Access VPN: Allows individual users to connect to a private network.
- Site-to-Site VPN: Connects two or more networks together over the internet.
VPNs are particularly effective in environments where employees need to access internal resources from remote locations. They provide a secure and scalable solution for remote login.
Configuring Firewalls for Remote Access
Proper firewall configuration is essential for enabling secure remote login device behind firewall access. Administrators must carefully define rules to allow legitimate traffic while blocking potential threats.
Best Practices for Firewall Configuration
- Use specific rules to allow only necessary ports and protocols.
- Regularly update firewall firmware and software to address vulnerabilities.
- Monitor firewall logs to detect and respond to suspicious activity.
A study by Gartner found that 99% of firewall breaches are caused by misconfigurations. Ensuring proper configuration is critical to maintaining network security.
Authentication Mechanisms for Secure Access
Authentication is a key component of securing remote login device behind firewall connections. Modern authentication mechanisms go beyond simple username and password combinations to include advanced techniques such as biometrics and hardware tokens.
Multi-Factor Authentication (MFA)
MFA adds an extra layer of security by requiring users to provide two or more verification factors to gain access. Common factors include:
- Something the user knows (password).
- Something the user has (smartphone or hardware token).
- Something the user is (fingerprint or facial recognition).
Implementing MFA significantly reduces the risk of unauthorized access and enhances overall security.
Tools and Software for Remote Login
There are numerous tools and software solutions available for remote login device behind firewall scenarios. Some popular options include:
TeamViewer
TeamViewer is a versatile remote access tool that supports cross-platform connectivity. It offers features such as file transfer, meeting functionality, and multi-monitor support.
AnyDesk
AnyDesk is another popular remote desktop solution known for its high performance and low latency. It uses advanced compression techniques to deliver fast and reliable connections.
Both tools provide robust security features and are widely used in enterprise environments.
Troubleshooting Common Issues
Despite careful planning and implementation, issues may arise when setting up remote login device behind firewall solutions. Common problems include:
- Connection Errors: Ensure all necessary ports are open and firewall rules are correctly configured.
- Authentication Failures: Verify user credentials and MFA settings.
- Performance Issues: Optimize network settings and reduce bandwidth consumption.
Regularly testing and monitoring remote access solutions can help identify and resolve issues before they impact productivity.
Future Trends in Remote Login Solutions
The landscape of remote login device behind firewall solutions is evolving rapidly. Emerging technologies such as zero-trust architecture and quantum encryption are shaping the future of secure remote access.
Zero-Trust Architecture
Zero-trust architecture assumes that threats exist both inside and outside the network. It requires continuous verification of every access attempt, regardless of the user's location.
Quantum Encryption
Quantum encryption promises to revolutionize data security by leveraging the principles of quantum mechanics. It offers unprecedented levels of security and resistance to future attacks.
Staying informed about these trends is essential for maintaining cutting-edge remote access solutions.
Conclusion and Next Steps
In conclusion, mastering remote login device behind firewall solutions requires a comprehensive understanding of firewalls, authentication mechanisms, and best practices. By implementing secure remote access solutions, organizations can enhance productivity while maintaining robust security.
We encourage readers to take the following actions:
- Review and update your firewall configurations regularly.
- Implement multi-factor authentication for all remote access points.
- Explore emerging technologies to stay ahead of potential threats.
Feel free to leave a comment or share this article with your colleagues. For more insights on cybersecurity and remote access, explore our other articles on the website.