Mastering IoT SSH Tunnel AWS: Your Ultimate Guide
IoT SSH tunnel AWS has become a cornerstone for secure communication in the world of connected devices. As the Internet of Things (IoT) continues to expand, ensuring secure data transfer between devices and cloud platforms is more critical than ever. This article will delve into the intricacies of IoT SSH tunnel AWS, providing you with the knowledge and tools to implement secure communication channels.
With the rise of smart homes, wearable technology, and industrial automation, IoT devices are generating massive amounts of data. However, transmitting this data securely remains a significant challenge. IoT SSH tunnel AWS offers a robust solution, enabling encrypted connections between IoT devices and the AWS cloud. This ensures that sensitive information remains protected from unauthorized access.
In this comprehensive guide, we will explore the concept of IoT SSH tunnel AWS, its benefits, implementation strategies, and best practices. Whether you're a developer, IT professional, or simply someone interested in IoT security, this article will provide valuable insights to help you harness the power of AWS for secure IoT communication.
Introduction to IoT SSH Tunnel AWS
IoT SSH tunnel AWS represents a secure method for connecting IoT devices to the AWS cloud infrastructure. SSH tunnels provide encrypted communication channels, ensuring that data transmitted between devices and servers remains confidential and tamper-proof. This approach is particularly valuable in scenarios where IoT devices operate in untrusted networks or require secure access to cloud-based resources.
Why Choose AWS for IoT SSH Tunnel?
AWS offers a scalable and reliable platform for managing IoT devices and their data. By integrating SSH tunnels with AWS services, organizations can achieve end-to-end encryption, enhanced security, and seamless device management. AWS also provides a suite of tools and services, such as AWS IoT Core and AWS Lambda, that streamline the development and deployment of IoT applications.
Key Features of IoT SSH Tunnel AWS
- End-to-end encryption for secure data transmission.
- Scalability to accommodate growing numbers of IoT devices.
- Integration with AWS services for enhanced functionality.
- Support for multiple protocols and architectures.
Understanding IoT Security
IoT security is a critical concern in today's interconnected world. With billions of devices communicating over the internet, the potential for cyberattacks and data breaches is significant. IoT SSH tunnel AWS plays a vital role in mitigating these risks by establishing secure communication channels.
Common IoT Security Challenges
- Data interception and eavesdropping.
- Unauthorized access to devices and networks.
- Firmware vulnerabilities and outdated software.
- Lack of standardized security protocols.
How IoT SSH Tunnel Enhances Security
SSH tunnels encrypt data at both ends of the communication channel, ensuring that even if intercepted, the data remains unreadable to unauthorized parties. This encryption, combined with AWS's robust security features, provides a comprehensive solution for protecting IoT devices and their data.
AWS IoT Core Overview
AWS IoT Core is a managed cloud service that allows connected devices to interact securely with cloud applications and other devices. It supports billions of devices and trillions of messages, making it an ideal platform for large-scale IoT deployments. When combined with IoT SSH tunnel AWS, it provides a powerful framework for secure communication.
Key Components of AWS IoT Core
- Device Gateway: Handles communication between devices and the cloud.
- Message Broker: Facilitates secure messaging using MQTT, HTTP, or WebSockets.
- Rules Engine: Processes and routes messages to other AWS services.
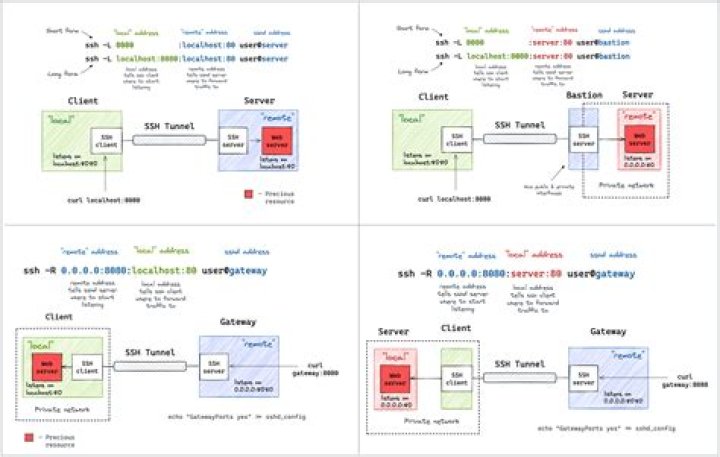
How SSH Tunnel Works
An SSH tunnel creates an encrypted connection between a client and a server, allowing secure transmission of data over untrusted networks. In the context of IoT SSH tunnel AWS, this involves establishing an SSH session between an IoT device and an AWS server, ensuring that all communication is encrypted and secure.
Steps to Establish an SSH Tunnel
- Install an SSH client on the IoT device.
- Generate SSH keys for authentication.
- Configure the SSH tunnel to connect to the AWS server.
- Route traffic through the tunnel for secure communication.
Benefits of Using SSH Tunnel with AWS
Implementing IoT SSH tunnel AWS offers numerous advantages, including enhanced security, scalability, and ease of integration. These benefits make it an attractive solution for organizations seeking to secure their IoT deployments.
Security Enhancements
SSH tunnels provide strong encryption and authentication mechanisms, ensuring that data remains secure during transmission. This is particularly important for sensitive applications, such as healthcare, finance, and industrial automation.
Scalability and Flexibility
AWS's cloud infrastructure supports large-scale IoT deployments, allowing organizations to scale their operations as needed. IoT SSH tunnel AWS ensures that this scalability does not come at the expense of security.
Steps to Implement IoT SSH Tunnel AWS
Implementing IoT SSH tunnel AWS involves several key steps, from setting up the AWS environment to configuring the SSH tunnel on IoT devices. Below is a step-by-step guide to help you get started.
Step 1: Set Up AWS Environment
Create an AWS account and set up the necessary services, such as AWS IoT Core and Amazon EC2. Ensure that security groups and network settings are properly configured to allow SSH access.
Step 2: Configure IoT Devices
Install an SSH client on each IoT device and generate SSH keys for secure authentication. Configure the devices to connect to the AWS server using the SSH tunnel.
Step 3: Test and Monitor
Test the SSH tunnel to ensure that data is being transmitted securely. Use AWS CloudWatch and other monitoring tools to track performance and identify potential issues.
Best Practices for Secure IoT Communication
To maximize the security benefits of IoT SSH tunnel AWS, it is essential to follow best practices for IoT communication. These practices include regular updates, strong authentication, and network segmentation.
Regular Software Updates
Keep all IoT devices and software up to date to address known vulnerabilities and improve security. Regular updates also ensure compatibility with the latest AWS services and features.
Strong Authentication Mechanisms
Use strong authentication methods, such as SSH keys or two-factor authentication, to protect against unauthorized access. Avoid using default passwords and ensure that credentials are stored securely.
Troubleshooting Common Issues
Despite careful planning and implementation, issues may arise when using IoT SSH tunnel AWS. Below are some common problems and solutions to help you troubleshoot effectively.
Connection Issues
If devices fail to connect to the AWS server, check the following:
- Ensure that the SSH service is running on the server.
- Verify that firewall and security group settings allow SSH traffic.
- Check the SSH configuration on the IoT device.
Data Transmission Errors
If data transmission errors occur, consider the following:
- Test the SSH tunnel using a simple data transfer to identify issues.
- Monitor network performance and adjust settings as needed.
- Review AWS logs for additional insights.
Real-World Use Cases
IoT SSH tunnel AWS has been successfully implemented in various industries, providing secure communication for a wide range of applications. Below are some real-world use cases that demonstrate its versatility and effectiveness.
Smart Home Automation
In smart home environments, IoT SSH tunnel AWS ensures that communication between devices and the cloud remains secure, protecting user privacy and preventing unauthorized access.
Industrial IoT
In industrial settings, IoT SSH tunnel AWS enables secure monitoring and control of critical infrastructure, reducing downtime and improving operational efficiency.
Future of IoT SSH Tunnel AWS
As IoT continues to evolve, the role of IoT SSH tunnel AWS will become increasingly important. Advances in encryption technology, quantum computing, and AI-driven security will further enhance its capabilities, ensuring that organizations can securely leverage the power of connected devices.
The future of IoT SSH tunnel AWS also includes greater integration with emerging technologies, such as 5G networks and edge computing, enabling faster and more reliable communication for IoT applications.
Kesimpulan
IoT SSH tunnel AWS represents a powerful solution for securing IoT communication in today's interconnected world. By leveraging the scalability and reliability of AWS, organizations can ensure that their IoT deployments remain secure and efficient. Following best practices and staying informed about the latest developments in IoT security will help you make the most of this technology.
We invite you to share your thoughts and experiences with IoT SSH tunnel AWS in the comments below. For more information on IoT security and AWS services, explore our other articles and resources. Together, let's build a safer and more connected future!